Trending Topics
Cisco Community is an active and collaborative place to learn more about our products and ask questions of peers and Cisco experts! Check out some of the most popular conversations happening right now!
-
Firepower with Duo Auth Proxy not working
by Pando -
ESA Cluster query
by Vishal6 -
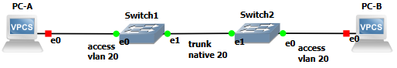
Data Encapsulation
by Tech enthusiast1 -
ACL is blocking HTTP(s) even though it is set to Permit
by Mike McCotter -
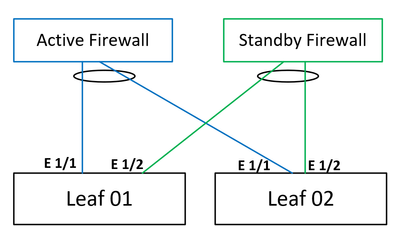
ACI L3out Pair Firewalls
by atalebzadeh -
CCNA and then? CyberOps? CCNP?
by LetMePass -
NCS2006 shelf menu
by ptate -
SNORT GID 2: Tagged Packets
by cpaquet